Issue 16
This issue is sponsored by Invary. Check out Invary's ability to detect hidden rootkits, a task that modern threat detection solutions fail in action » HERE.
This week TLDR i.e. 2 minutes version (For executives):
AWS Systems Manager Patch Manager now supports instances running RHEL 8.8, MacOS Monterey & Ventura.
AWS announces the general availability of multi-VPC elastic network interface (ENI) attachments for EC2 instances.
Trending in Cloud & Cyber Security (News, Blogs, Tweets etc):
AWS Security Blogs (& Bulletins):
AWS Digital Sovereignty Pledge: Announcing a new, independent sovereign cloud in Europe. Link.
AWS FedRAMP Revision 5 baselines transition update. Link.
Mask and redact sensitive data published to Amazon SNS using managed and custom data identifiers. Link.
The security attendee’s guide to AWS re:Invent 2023. Link.
A phased approach towards a complex HITRUST r2 validated assessment. Link.
CISA Announces New Release of Logging Made Easy- a Windows-based, free and open log management solution. Link.
Tool: Aquia SCPKit. SCPs have a current limit of 5 total per entity, and a size limit on each of 5120 characters. This tool will merge selected SCPs into the fewest amount of policies, and optionally remove whitespace characters as they count toward the character limit. Git Link.
Windows 11: SMB now supports requiring encryption of all outbound SMB client connections. With this new option, administrators can mandate that all destination servers use SMB 3 and encryption, and if missing those capabilities, the client won’t connect. Link.
This week Long i.e. 5-10 minutes version (For architects & engineers):
AWS Systems Manager Patch Manager now supports instances running Red Hat Enterprise Linux (RHEL) 8.8, MacOS Monterey, and MacOS Ventura. Link.
AWS customers using the AWS Console Mobile App for iOS can now use their mobile device’s password manager for faster sign in, set a default AWS identity for quicker recurring access to their resources, and use supported virtual authenticator apps, FIDO security keys and hardware TOTP tokens for multi-factor authentication (MFA). Link.
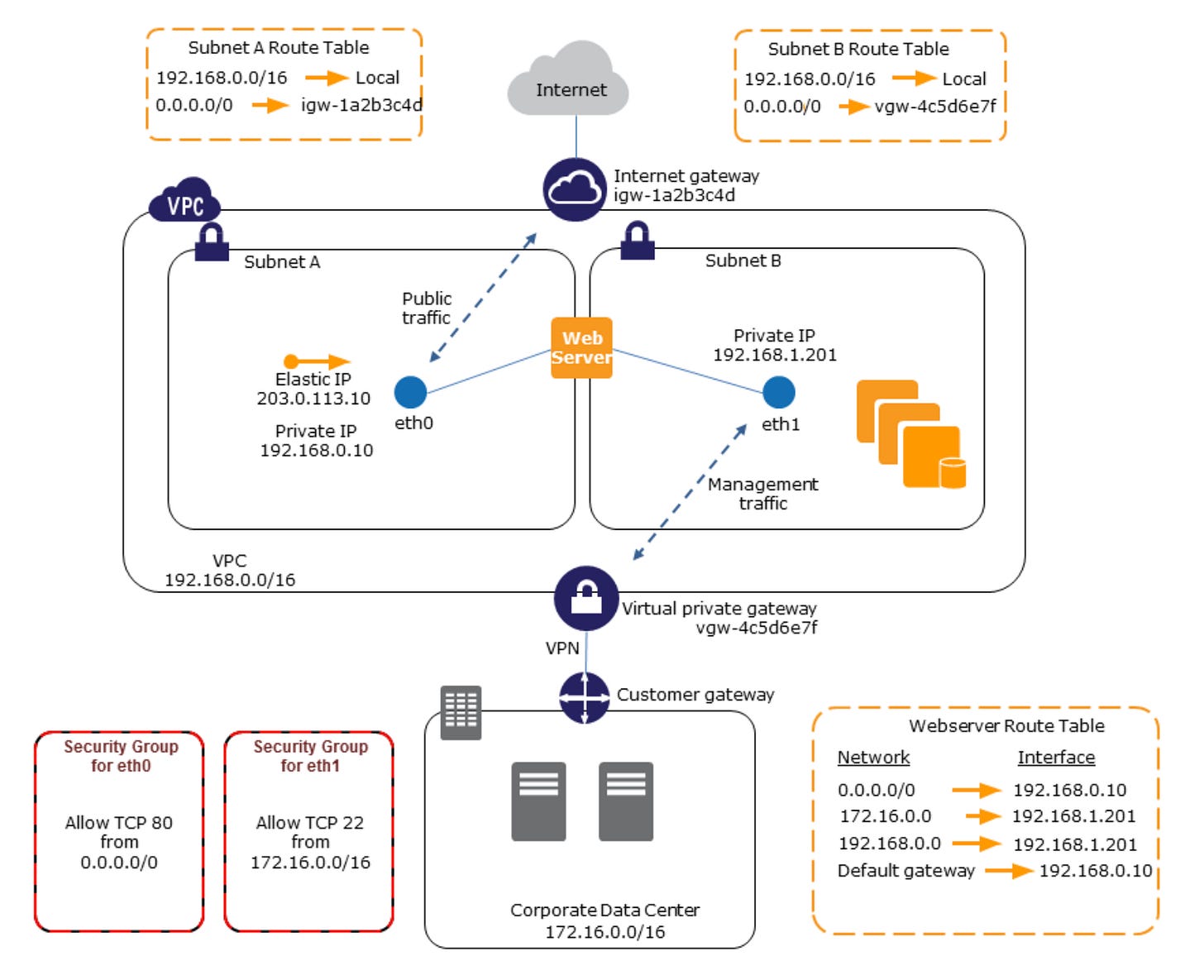
AWS has introduced a feature enabling the attachment of multiple elastic network interfaces (ENIs) to Amazon Elastic Compute Cloud (EC2) instances within Virtual Private Clouds (VPCs). This new capability allows customers to launch EC2 instances with a primary ENI in one VPC and then attach a secondary ENI from a different VPC. By leveraging multi-VPC ENI attachments, customers can uphold VPC-level separation between networks while still facilitating communication between specific workloads, such as centralized appliances and databases. For certain customers like telecommunications providers who route various types of network traffic both within AWS regions and between on-premises and AWS, it is essential to have a logical separation for their workloads. By utilizing distinct VPCs for different categories of network traffic, like control and data plane traffic, customers can now segregate their traffic at the VPC level. Meanwhile, shared workloads like virtual routers, firewalls, and databases can sustain connectivity between these separate VPCs. With the introduction of multi-VPC ENI attachments, customers can run interconnected workloads across these otherwise isolated VPCs, ensuring that specific functions can communicate with each VPC. Link.
Thank You for reading! If you enjoyed this newsletter, I’d be grateful if you could forward it to your professional circle.
Best,
AJ