Issue 18
This issue is sponsored by Invary. Check out Invary's ability to detect hidden rootkits, a task that modern threat detection solutions fail in action » HERE.
This week TLDR i.e. 2 minutes version (For executives):
AWS announced the ability to disable public sharing of new & existing EBS snapshots.
AWS KMS is now FIPS 140-2 Security Level 3.
EC2 Image Builder now supports Amazon Linux 2023 & Ubuntu 22.04 LTS.
Amazon GuardDuty introduces new machine learning capability to enhance threat detection for Amazon EKS detections.
Trending in Cloud & Cyber Security (News, Blogs, Tweets etc):
AWS Security Blogs (& Bulletins):
AWS KMS is now FIPS 140-2 Security Level 3 (NIST link). What does this mean for you? Link
How to improve your security incident response processes with Jupyter notebooks. Link.
Build an entitlement service for business applications using Amazon Verified Permissions. Link.
Set up AWS Private Certificate Authority to issue certificates for use with IAM Roles Anywhere. Link.
Microsoft to roll out MFA-enforcing policies for admin portal access. Blog Link.
This week Long i.e. 5-10 minutes version (For architects & engineers):
The EC2 Image Builder service, designed to simplify and expedite the construction, customization, and upkeep of Virtual Machine images, now extends its support to additional Operating Systems - Amazon Linux 2023 and Ubuntu 22.04 Long Term Support (LTS). Users can incorporate these newly added managed images as a foundational element in their image pipelines, allowing them to create and manage customized images in a manner akin to the process used for supported Windows and Linux operating systems. EC2 Image Builder serves as a comprehensive solution for automating various image management tasks, including creation, patching, testing, distribution, and sharing. Clients can establish an automated pipeline to generate secure and current Linux and Windows Server images. As software updates become available, Image Builder can autonomously generate a new image, conduct tests, and distribute the resulting image to specified AWS regions. Link.
Amazon GuardDuty has integrated advanced machine learning techniques to enhance the precision of detecting abnormal activities that may indicate potential threats to your Amazon Elastic Kubernetes Service (Amazon EKS) clusters. This enhanced capability involves continuous modeling of Kubernetes audit log events from Amazon EKS, enabling the identification of highly suspicious actions. Examples of such activities include unusual user access to Kubernetes secrets, which could be exploited for privilege escalation, and the detection of suspicious container deployments featuring images not commonly utilized in the cluster or account. These new threat detection features are accessible to all GuardDuty customers with GuardDuty EKS Audit Log Monitoring ‘enabled’. The novel machine learning approach establishes a baseline for normal behavior, considering factors such as pod or container configuration, autonomous system number (ASN), or user agent. This enables GuardDuty to more precisely pinpoint abnormal activities within your Amazon EKS clusters related to recognized attack tactics, including discovery, credential access, privilege escalation, and execution. Link.
Amazon Elastic Block Store (EBS) has introduced support for Block Public Access concerning EBS Snapshots. This security feature, applicable across an entire AWS account, empowers customers to restrict the public sharing of EBS Snapshots within a specific AWS Region. For those overseeing EBS Snapshots at scale, this presents a straightforward and proactive measure to protect their data from unintentional access by unauthorized individuals. EBS Snapshots are commonly utilized by customers for tasks such as backing up EBS volumes for disaster recovery, data migration, and compliance purposes. The introduction of Block Public Access for EBS Snapshots adds an extra layer of security, mitigating the risk of unauthorized access and potential misuse of snapshot data. The setting offers two modes: 'block new sharing' and 'block all sharing.' Activation of Block Public Access in either mode automatically prevents any future attempts to make a snapshot public. Moreover, when 'block all sharing' mode is active, customers can restrict public access to any existing public snapshots. This, combined with the recently launched Block Public Access for EC2 AMIs, provides customers with a comprehensive means to prevent public access to their EBS Snapshots. It's important to note that Block Public Access for EBS Snapshots is initially deactivated for all AWS accounts. Customers can enable this setting through the AWS Console, AWS Command Line Interface (CLI), and AWS SDKs according to their preferences. Blog.
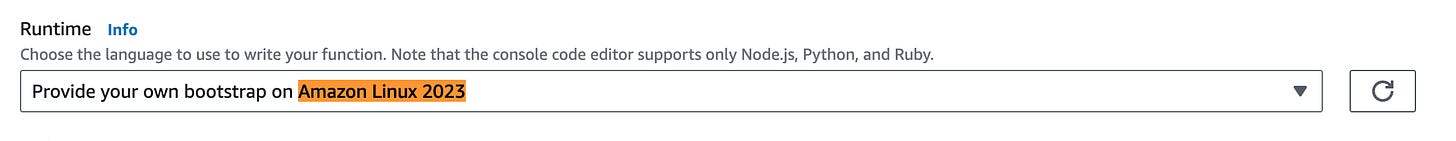
AWS Lambda has introduced support for Amazon Linux 2023, serving as both a managed runtime and a container base image. This runtime boasts a significantly reduced deployment footprint compared to Amazon Linux 2 runtimes and offers updated versions of essential libraries like glibc. Furthermore, the Amazon Linux 2023 runtime forms the foundation for upcoming Lambda runtime releases, including Node.js 20, Python 3.12, Java 21, and .NET 8. Detailed information can be found in our blog post titled "Amazon Linux 2023 runtime now available on AWS Lambda. The Amazon Linux 2023 runtime establishes an OS-only execution environment for Lambda functions, building upon the AL2023 minimal container image release. This OS-only Lambda environment proves beneficial in three specific scenarios: when utilizing languages compiled to native code, such as Go or Rust; when employing third-party runtimes like Bref for PHP; or when utilizing custom runtimes. AWS will automatically apply updates and security patches to both the managed runtime and container base image as they become available. Link.
Amazon CloudFront introduces a consolidated security dashboard, allowing you to seamlessly activate, oversee, and oversee standard security safeguards for your web applications directly through the Amazon CloudFront console. Tailored for customers seeking an integrated approach to managing both application delivery and security, this interactive security dashboard integrates AWS WAF visibility and controls directly into your CloudFront distribution. It provides insights into your application's primary security trends, permitted and denied traffic, and bot activities. The dashboard also incorporates investigative tools like a visual log analyzer and built-in blocking controls, streamlining the process of identifying traffic patterns and blocking unwanted traffic without the need for extensive log querying or security rule creation. Crafted for simplicity and convenience, the CloudFront security dashboard facilitates the activation of standard security measures, real-time monitoring and investigation of traffic, and the mitigation of anomalies and threats. The unified experience revolves around user-friendly workflows, enabling you to make decisions and take actions without delving into the complexities of writing security rules. For instance, you can visually search AWS WAF logs stored in Amazon CloudWatch without the need for manual queries. The investigative process is further simplified through dynamic visual cues, such as aggregation by IP address, country, HTTP method, and URI path. Additionally, visual blocking actions allow for easy application of mitigating measures with just one click. Blog Link.
AWS KMS is now FIPS 140-2 Security Level 3 (NIST link). This means, customers who previously needed to meet compliance requirements for FIPS 140-2 Level 3 on AWS were required to use AWS CloudHSM but now can use AWS KMS by itself for key generation and usage. Compared to CloudHSM, AWS KMS is typically lower cost and easier to set up and operate as a managed service.
Thank You for reading! If you enjoyed this newsletter, I’d be grateful if you could forward it to your professional circle.
Best,
AJ