Issue 30 & 31
This issue combines the skipped Issue 30 (from last week) hence it will be longer in length than usual Issues.
This issue is sponsored by Invary. Check out Invary's ability to detect hidden rootkits, a task that modern threat detection solutions fail in action » HERE.
This week TLDR i.e. 1 minutes version (For executives):
Reminder: Effective February 1, 2024 there will be a charge of $0.005 per IP per hour for all public IPv4 addresses, whether attached to a service or not. Link.
AWS announces support for logging AWS AppConfig data events in AWS CloudTrail.
AWS Control Tower receives DoD Impact Level 4 and 5 authorization.
AWS AppFabric is now ISO, PCI, and SOC compliant.
Amazon Cognito adds signing, encryption, and Identity Provider-initiated SSO for SAML federation.
Announcing Single sign-on (SSO) support for JetBrains IDE within Amazon CodeCatalyst.
Announcing support for IdP-initiated SSO with Amazon WorkSpaces Web.
AWS Application Load Balancer announces one-click WAF integrations.
Amazon SQS launches the Extended Client Library for Python to support payloads up to 2GB.
AWS WAF announces Captcha improvements.
Amazon GuardDuty Malware Protection now supports scanning EBS managed key encrypted volumes.
AWS IoT Core supports Online Certificate Status Protocol Stapling for server certificates.
Trending in Cloud & Cyber Security (Security Blogs, articles, news, advisories etc):
AWS Security Blogs & Bulletins:
Data masking and granular access control using Amazon Macie and AWS Lake Formation. Link.
How to migrate your on-premises domain to AWS Managed Microsoft AD using ADMT. Link.
How to migrate asymmetric keys from CloudHSM to AWS KMS. Link.
How to enforce creation of roles in a specific path: Use IAM role naming in hierarchy models. Link.
Import entire applications into AWS CloudFormation. Link.
AWS Security Bulletin: CVE-2024-21626 - Runc container issue. Link. Customer action requested of you use: Amazon Linux, Bottlerocket OS, ECS, EKS, AWS Elastic Beanstalk, Finch, AWS Deep Learning AMI, AWS Batch, Amazon SageMaker.
General security blogs, articles & reports:
State of API Security 2024- The API Secret Sprawl by Escape. PDF here.
Article by Nick Frichette on ‘Abusing Misconfigured Role Trust Policies with a Wildcard Principal’. Link. Also check, ‘Evading Logging in the Cloud: Bypassing AWS CloudTrail’ BlackHat YouTube presentation HERE.
Interesting read with great humor. Daniel Grzelak’s ‘Conditional Love for AWS Metadata Enumeration’. Link.
Super interesting one. ‘The curious case of DangerDev@protonmail.me.’-An AWS incident response story by Invictus IR. Link.
A Year of Disruption and Resilience: The Cybersecurity Market in 2023 by Mike Privette. Link.
CloudFlare blog on it’s Thanksgiving 2023 security incident. Link.
Cool article. Datadog- ‘An analysis of a TeamTNT doppelgänger’ by Frederic Baguelin, Andy Giron, Zack Allen and Christophe Tafani-Dereeper. Link.
Wiz- Leaky Vessels: runC and BuildKit container escape vulnerabilities - everything you need to know’. Link.
Trending on the news & advisories:
GitLab Critical Security Release. Link.
Florida Man Charged in SIM-Swapping Spree is Key Suspect in Hacker Groups Oktapus, Scattered Spider. Link.
Qualys TRU Discovers Important Vulnerabilities in GNU C Library’s syslog(). Link.
Ivanti- (Additional announcements) CVE-2024-21888 Privilege Escalation for Connect & Policy Secure. Link. Additionally CISA directive: Agencies were required to disconnect all instances of Ivanti Connect Secure and Ivanti Policy Secure solution products by 11:59PM on Friday February 2, 2024. Link.
CISA new known Vulnerability- CVE-2022-48618. An attacker with arbitrary read and write capability may be able to bypass Pointer Authentication. Link.
This week Long i.e. 5-10 minutes version (For architects & engineers):
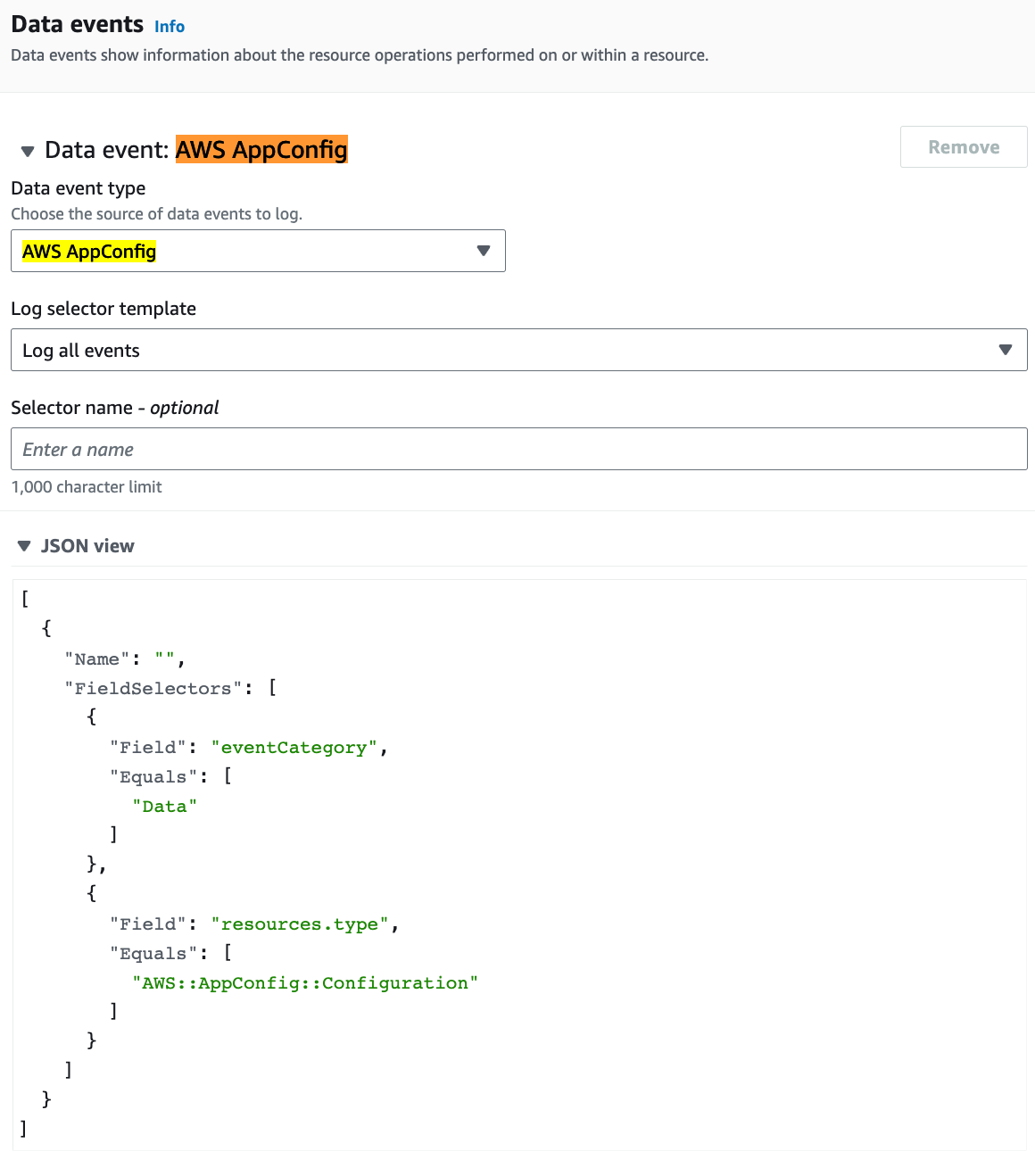
AWS AppConfig has introduced support for AWS CloudTrail data event logging for
StartConfigurationSessionandGetLatestConfigurationAPIs ( data plane request) in AWS CloudTrail logs. This information encompasses details like the IAM identity responsible for the request, the timestamp of the request, the AWS AppConfig resources linked to the request, and whether the request was initiated by the AWS AppConfig Agent. Link. For example, this is my event data store sample:AWS Control Tower is authorized for Department of Defense Cloud Computing Security Requirements Guide Impact Levels 4 and 5 (DoD SRG IL4 and IL5) in the AWS GovCloud (US-East and US-West) Regions. Link.
AWS AppFabric now adhere to the standards set by the International Organization for Standardization (ISO), Payment Card Industry Data Security Standard (PCI), and Service Organization Control (SOC I, II, and III) requirements. Link.
Amazon Cognito has introduced three enhancements for users employing the SAML standard for federation. Users now have the capability to utilize Amazon Cognito user pools for transmitting signed SAML authentication requests, mandating encrypted responses from a SAML identity provider, and implementing identity provider-initiated single sign-on (SSO) for SAML federation. Link. For example, this is my setting under the Cognito user pool identity provider.
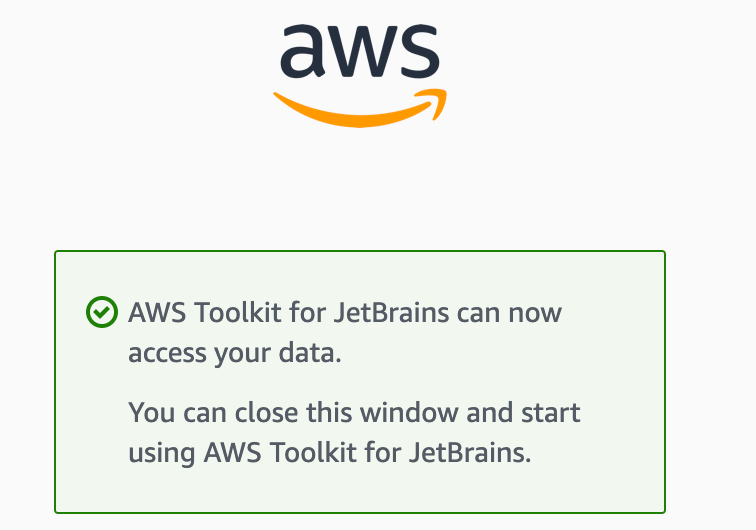
AWS has introduced support for single sign-on in conjunction with JetBrains IntelliJ, GoLang, and PyCharm IDEs when using Amazon CodeCatalyst development environments. This release enables users who have configured AWS IAM Identity Center with CodeCatalyst to manage supported JetBrains development environments within their CodeCatalyst projects, including actions such as creating, deleting, pausing, and resuming. Link. For example, in my Mac Silicon JetBrains Gateway, I was able to install Amazon CodeCatalyst plugin and connect to CodeCatalyst using my AWS SSO (Identity Center). Auth process is similar to login to AWS SSO via terminal using “aws configure sso” (Note: The SSO Jetbrains IDE SSO feature is available in the US West (Oregon) and Europe (Ireland) regions.)
Amazon WorkSpaces Web announced support for identity provider (IdP) initiated single sign on (SSO) for standard authentication web portals. IdP-initiated SSO support provides administrators with more options in defining the sign in flow for their users. Link. Here’s my setting initiation example. (Note: IdP-initiated SSO for standard authentication portals is available in only limited AWS regions. My AWS Identity Center is in Ohio (us-east-2) region so I wasn’t able to set AWS IAM Identity Center.)
AWS Application Load Balancer (ALB) has introduced console integration with AWS WAF, facilitating the easy securing of your applications behind ALB with just a single click. This integration serves as a primary defense layer against common web threats for ALB-utilizing applications by enabling AWS WAF protections. Optionally, you can further customize protection settings, such as bot detection and fraud prevention, for your applications through the AWS WAF console. Link. For example, under my ALB, I was able to see the option. It took about 2 minutes for the deployment.
Amazon Simple Queue Service (SQS) has introduced an open-source Extended Client Library for Python, enabling the transmission and reception of sizable message payloads. With the Extended Client Library for Python, you can now handle messages exceeding 256KB, extending up to a maximum of 2GB. This library stores the actual payload in an Amazon S3 bucket and dispatches a message containing a reference to the stored S3 object to an Amazon SQS queue. Furthermore, SQS already supports the Extended Client Library for Java. Users can now efficiently distribute large messages to SQS through the Amazon Simple Notification Service (SNS) using either the Extended Client Library for Python or Java. Link. Github Link. I tried it using the sample python code below which basically creates an Amazon S3 bucket with a random name, an Amazon SQS queue named
MyQueueand sends a message that is stored in an S3 bucket and is more than 256 KB to the queue. Finally, the code retrieves the message, returns information about it, and then deletes the message, the queue, and the bucket. I was able to verify the events from CloudTrail.AWS WAF Captcha now includes audio Captcha support in eight additional languages, introducing a new Captcha type for improved usability, along with the introduction of revocable API keys. By expanding language support, introducing a fresh Captcha puzzle, and offering the ability to quickly disable compromised keys, WAF Captcha delivers advanced features to globally safeguard web applications. To begin, audio Captchas now support eight additional languages. This expansion broadens language accessibility for users solving audio Captchas. Next, AWS WAF has introduced a novel Captcha puzzle known as Grid Captcha. This puzzle displays a grid of images, requiring users to select those corresponding to a specified category, leveraging the visual and categorical skills of authentic humans in distinguishing from bots. The Grid Captcha enhances pass-through rates, contributing to a more user-friendly experience. Lastly, administrators can fortify the security posture by promptly deactivating or rotating API keys before their expiration. This proactive measure helps prevent the abuse of leaked keys by swiftly revoking access. API keys can be disabled via the WAF Console, AWS SDK, or CLI, empowering administrators with a versatile means of control. Link.
Amazon GuardDuty Malware Protection has expanded its capabilities to scan Amazon Elastic Block Store (Amazon EBS) volumes. This includes encrypted volumes with EBS managed keys attached to EC2 instances and container workloads, alongside unencrypted EBS volumes and those encrypted with AWS KMS customer-managed keys (CMKs). Users can now configure automatic malware scanning based on GuardDuty network-based findings and initiate on-demand malware scans specifically for EBS volumes encrypted with EBS managed keys. In the event of potential malware detection, GuardDuty generates actionable security findings that include details such as the threat and file name, file path, Amazon EC2 instance ID, resource tags, and, for containers, the container ID and the container image used. This information aids customers in identifying and responding to malware security findings. Importantly, GuardDuty Malware Protection doesn't require the deployment of additional security agents or software and is designed to have no performance impact on running workloads. Link. For example, I had an EC2 with encrypted EBS and was successfully able to initiate a on-demand scan. (Note: All screenshots in the newsletter are from a lab AWS account & are decommissioned. The author is aware of any information that’s not masked).
AWS IoT Core, the managed cloud service facilitating secure connections of Internet of Things (IoT) devices to the cloud at scale, now supports Online Certificate Status Protocol (OCSP) Stapling for TLS X.509 Server Certificates using Custom Domains and Configurable Endpoints. This new feature empowers customers to enhance the verification process for the validity of their custom domain's server certificate, allowing for quicker responses to server certificate revocations, for instance. By incorporating the OCSP response with the certificate during the TLS handshake, the need for a separate client request to an OCSP server is eliminated, leading to faster connection establishment. Link. For example, I tried the OCSP option under domain configuration
© 2024 aws-cloudsec, LLC