Issue 8
Release Date: September 04, 2023
This week TLDR i.e. 2 minutes version (For executives):
AWS Systems Manager Patch Manager now supports instances running RHEL 8.7, 9.[0,1,2] Rocky Linux 8.[6,7], 9.[0,1,2] and Oracle Linux 8.6, 8.7, 9.[0,1,2].
AWS Private Certificate Authority launches Connector for Active Directory.
AWS Transfer Family announces multiple methods to authenticate SFTP users.
You can now route any IPv4 and IPv6 traffic entering your Amazon VPC from virtual private gateway through a Gateway Load Balancer endpoint before the traffic reaches the destination.
AWS Amplify supports time-based one-time password for MFA on Android, Swift, Flutter.
App Runner adds support for Bitbucket source code repository.
AWS Outposts rack now supports intra-VPC communication across multiple Outposts.
AWS Firewall Manager now supports identifying excessively permissive rules that permit traffic from all IP ranges. You can detect and remediate 0.0.0.0/0 and ::/0 CIDRs in a Security Group using the Security Group Content Audit policy.
Amazon SES now offers email delivery and engagement history for every email.
AWS Directory Service for Microsoft Active Directory and AD Connector are integrating with AWS Private Certificate Authority to issue certificates for domain-joined objects that use Active Directory (AD) auto-enrollment.
Trending in Cloud & Cyber Security (News, Blogs etc):
Fig has joined AWS. Link.
Mozilla has released security updates to address vulnerabilities for Firefox 117, Firefox ESR 115.2, Firefox ESR 102.15, Thunderbird 115.2, and Thunderbird 102.15. A cyber threat actor can exploit some of these vulnerabilities to take control of an affected system. CISA Link.
VMware has released security updates to address multiple vulnerabilities in Aria Operations for Networks. A cyber threat actor can exploit one of these vulnerabilities to take control of an affected system. CISA encourages users and administrators to review VMware Security Advisory VMSA-2023-0018 and apply the necessary updates. CISA Link.
2024 Apple Security Research Device Program now accepting applications. Link.
Really cool blog on “Getting into AWS cloud security research as a n00bcake” by Daniel Grzelak. Blog Link. You can find Daniel in Twitter (X) here @dagrz.
AWS labs threat-composer- A simple threat modeling tool to help humans to reduce time-to-value when threat modeling. Git link.
CISA- Infamous Chisel Malware Analysis Report. Link.
This week Long i.e. 5-10 minutes version (For architects & engineers):
AWS Private Certificate Authority (AWS Private CA) now offers the Connector for Active Directory (AD), simplifying the integration of AWS Private CA into your Windows environments managed through AD. This integration eliminates the need for local agent deployment, patching, or proxy server updates. The Connector for AD enables the issuance of certificates for identifying domain-joined objects, such as users, computers, and smart cards utilizing AD auto-enrollment. When used in conjunction with AWS Managed Microsoft AD, it facilitates the migration of your AD and public key infrastructure to the cloud, eliminating on-premises infrastructure requirements. Link.
Amazon VPC Container Networking Interface (CNI) Plugin now includes support for Kubernetes NetworkPolicy resources. This means customers can use the same Amazon VPC CNI for both pod networking and network policies in their Kubernetes clusters, streamlining the need for additional network access control software. This integration works seamlessly with existing VPC CNI capabilities.
Typically, in Kubernetes, pods can communicate freely within a cluster, but NetworkPolicy allows administrators to define communication rules for better network isolation. However, implementing NetworkPolicy often requires third-party plugins, leading to operational overhead and costs. With Amazon VPC CNI's NetworkPolicy support, AWS Kubernetes users can now easily control pod-to-pod traffic based on label selectors, namespaces, IP blocks, and ports with minimal complexity. They can use standard components like security groups and network access control lists (ACLs) for added security. Furthermore, customers can trace and troubleshoot policies at both cluster and node levels using the Amazon VPC CNI plugin. This feature is available in VPC CNI v1.14 and onwards for new clusters running Kubernetes version 1.25 and above, although it is initially turned off by default. Link.
AWS Transfer Family now provides the capability for customers to mandate both SSH key and password authentication when users connect to their SFTP servers. This added authentication layer enhances data security when granting user access to files. Previously, users could be authenticated using either their public key or password. With this enhancement, both methods can now be required simultaneously during a single session. This flexibility in authentication methods empowers organizations in various sectors, including financial services, healthcare, and the public sector, to align with internal security policies and enhance the protection of sensitive data. Link.
(Note: Since this is a cloud security focused blog, wanted to share that I use test accounts for all my blogs. I don’t deliberately usually blur/hide certain information when posting screenshots for clarity reasons. For example, I understand that, if your S3 bucket has certain public permissions, your AWS Account ID can be enumerated. Not that Account ID is a sensitive information itself, IMHO).
You now have the capability to direct both IPv4 and IPv6 traffic entering your Amazon Virtual Private Cloud (VPC) through a Gateway Load Balancer endpoint, which acts as an intermediary before reaching its final destination. This Gateway Load Balancer Endpoint can be used to process your VPC traffic through AWS Network Firewall or other security appliances available on the AWS Marketplace.
This enhancement allows you to route traffic originating from your virtual private gateway and entering your Amazon VPC through a Gateway Load Balancer Endpoint before it proceeds to its ultimate destination. Link . For detailed steps, check the launch Blog.
The Android, Swift, and Flutter libraries have incorporated Time-Based One-time Passwords (TOTP) as a multi-factor authentication (MFA) method. This enhancement empowers developers to offer their users a secure means of confirming their identity once they've provided their username and password.
Apps that leverage TOTP can now allow their users to link their apps to an Authenticator application, such as Google Authenticator, Authy, or Microsoft Authenticator. Following the user's entry of their username and password, they will be prompted to complete their sign-in by inputting the code generated by their chosen Authenticator app. Link. Blog link.
AWS App Runner has introduced the capability to deploy services directly from source code stored in a Bitbucket repository. To initiate the deployment of your source code to an App Runner service from Bitbucket, the first step is to establish a Bitbucket connection resource. You can create this resource using the App Runner console or the CreateConnection API. This was pretty straight forward. The console would redirect you to connect to a bitbucket account. Link.
You can now configure routes within your AWS Outposts rack subnet route table to facilitate traffic routing between subnets within the same VPC that spans across different Outposts, utilizing the Outpost local gateways (LGW). The LGW serves as the conduit for connectivity between your Outpost subnets and your on-premises network. This enhancement allows you to establish intra-VPC instance-to-instance IP communication across Outposts via direct VPC routing (DVR). Previously, to enable communication between instances across different Outposts, you had to create subnets in separate VPCs or use distinct IP address ranges/CIDRs, known as CoIP pools. With this update, you can now employ a unified VPC architecture for facilitating communication between instances across different Outposts while utilizing DVR, eliminating the need to manage separate VPCs and CoIP pools. This feature enables you to construct multi-Availability Zone (AZ)-like architectures for your on-premises applications running on Outposts racks connected to two different AZs. Link. Blog Link.
AWS Firewall Manager enhances its auditing capabilities for Security Groups by identifying overly permissive rules that allow traffic from all IP ranges. This improvement enables customers to detect and rectify the presence of 0.0.0.0/0 and ::/0 CIDRs within a Security Group using the Security Group Content Audit policy. Previously, AWS Firewall Manager offered the option to audit IP addresses falling within specific defined ranges. This new functionality streamlines security posture management by identifying and addressing these commonly encountered IP ranges. Link.
AWS ParallelCluster 3.7 is now available, introducing several important features:
Support for Ubuntu 22 and login nodes, allowing user access to be separated from the cluster's head node, reducing resource contention. Link.
Amazon S3 has introduced support for Multivalue Answer (MVA) in response to DNS queries for S3 endpoints. With MVA, you can now receive up to eight S3 IP addresses for each DNS query. These IP addresses can be leveraged to establish multiple concurrent connections to S3, leading to enhanced throughput. MVA also enhances retry mechanisms as applications can automatically attempt an alternative IP address without waiting for another DNS query. The newer versions of AWS SDKs, including Java 2.x, C++, and Python (Boto3), seamlessly benefit from MVA, requiring no adjustments to your application. If you are using the Java SDK v2 with the Common Runtime (CRT) library for asynchronous operations, MVA offers added advantages. CRT provides an alternative S3 asynchronous client that optimizes object transfers to and from S3 by automatically utilizing S3's multipart upload API and byte-range fetches. Additionally, CRT enhances reliability by automatically retrying individual failed parts of a file transfer without restarting the entire transfer. When combined with MVA, these retries are directed to alternative IP addresses, further enhancing the reliability of your connections to S3. Link. Blog Link.
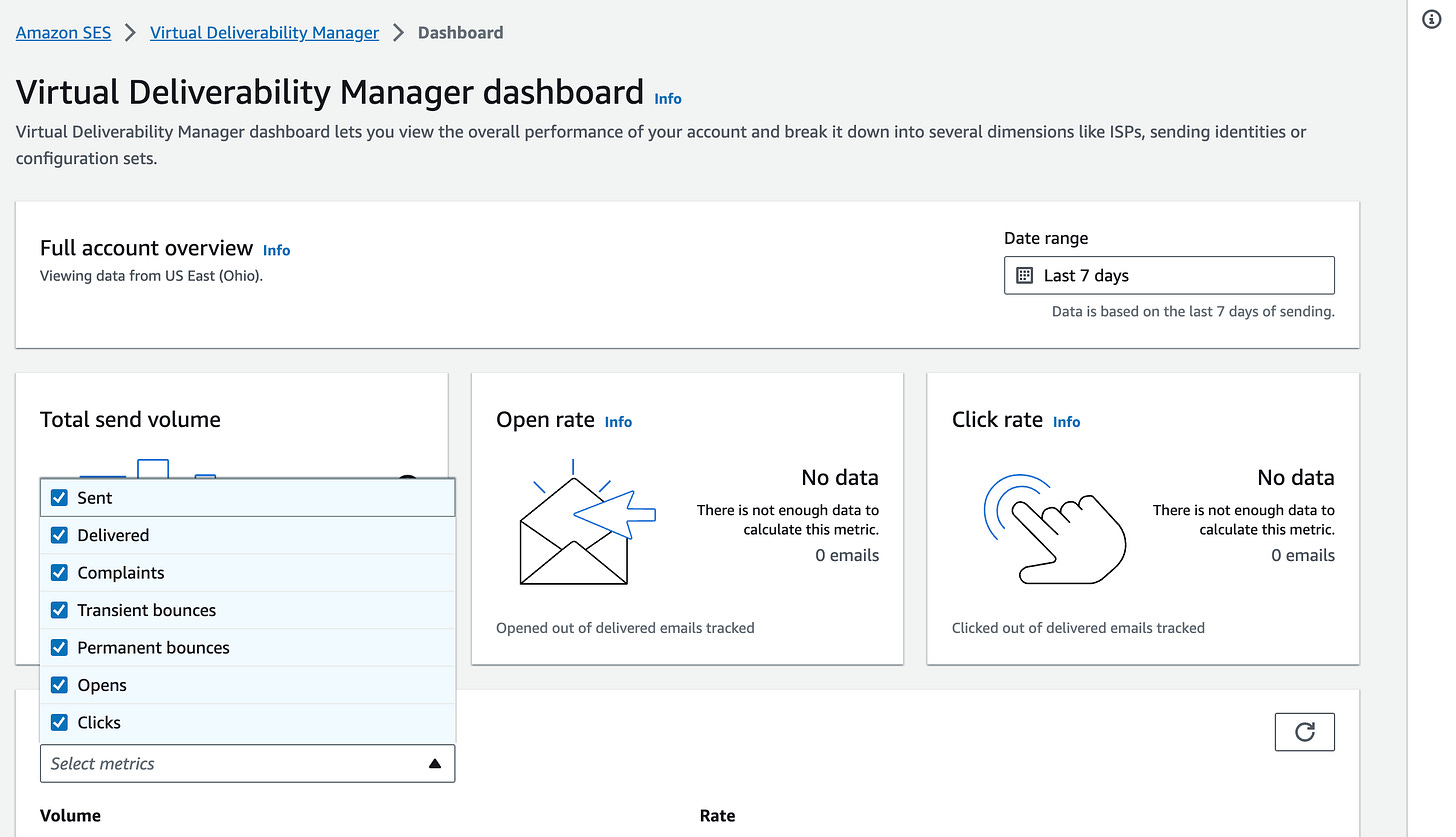
Amazon Simple Email Service (SES) has introduced a new deliverability feature that empowers customers to address individual email delivery issues, validate the delivery of critical messages, and pinpoint engaged recipients on a highly detailed, per-email basis. Senders can now delve into delivery performance trends and access delivery and engagement status for each email sent through SES. This enhancement streamlines the management and optimization of delivery and campaign performance with the assistance of the Virtual Deliverability Manager. Previously, SES' Virtual Deliverability Manager enabled email senders to identify general email delivery issues concerning inbox placement and engagement through metrics like bounce rates, opens, and clicks. Now, customers can leverage the Virtual Deliverability Manager dashboard to examine the status of every email dispatched via SES. Users can search for emails based on various criteria, including sender, send date, delivery status, subject line, and open and click status. This provides customers with a wide array of options for investigating email delivery and engagement, such as confirming the delivery of an order confirmation email, diagnosing low delivery success rates by scrutinizing mailbox provider response messages for bounced emails, or creating recipient lists for marketing follow-up initiatives. Link. Setting up was pretty straight forward. I didn’t have enough metrics/logs to demo but I can see a use case, especially from security team’s perspectives, for example, during investigations/incidents.
AWS Directory Service for Microsoft Active Directory (AWS Managed Microsoft AD) and AD Connector are now seamlessly integrating with AWS Private Certificate Authority (AWS Private CA) to facilitate the issuance of certificates for domain-joined objects employing Active Directory (AD) auto-enrollment. This integration allows you to adopt a fully managed AWS Private CA as a hassle-free substitute for your self-managed enterprise Certificate Authorities (CAs), eliminating the complexities of deploying, patching, or updating local agents or proxy servers. Additionally, this integration expedites the migration of AD-aware workloads to AWS. Setting up AWS Private CA integration with your directory is a straightforward process, requiring just a few clicks. You can establish this integration programmatically or through APIs using the AWS Private CA Connector. AWS Private CA takes on the responsibility of issuing and managing certificates for your directory objects, including users, groups, and machines, whether you are utilizing AWS Managed Microsoft AD directly or your self-managed AD through AD Connector. Link.
Security Jobs (Occasional post):
Adobe- Sr. Security Technical Program Manager- USA. Link.
Adobe- Sr Software Engineer, Security Tools- USA- Remote). Link.
Go Daddy- Distinguished Security Engineer. USA- Remote. Link.
Thank You for reading! If you enjoyed this newsletter, I’d be grateful if you could forward it to your professional circle.
Best,
AJ